Technology
The Rise of Web3 Developers: Why This Career Path is the Future of Tech

As technology advances, the internet is undergoing a revolutionary shift toward decentralization. Known as Web3, this next phase of the internet is redefining how we interact with digital systems by emphasizing transparency, user ownership, and autonomy.
At the heart of this evolution are Web3 developers—professionals whose expertise in blockchain and decentralized systems is driving innovation and creating exciting new opportunities. Pursuing a Web3 career is not just about adapting to industry trends; it’s about shaping the future of technology. In this article, we’ll explore why Web3 developers are in high demand and how you can step into this promising field.
What is Web3?
Web3 represents the decentralized evolution of the internet. Unlike its predecessor, Web2, where centralized platforms dominate, Web3 leverages blockchain technology to create an ecosystem that is transparent, secure, and community-driven.
Some of the defining features of Web3 include:
- Decentralization: Control is distributed among users rather than being concentrated in a single organization.
- Transparency: Blockchain technology ensures that all transactions and operations are open and verifiable.
- Automation: Smart contracts allow for self-executing agreements, reducing the need for intermediaries.
This paradigm shift has unlocked immense opportunities, particularly for developers who can create, manage, and enhance Web3 applications.
Why a Web3 Career is the Future
- Rapid Growth in Blockchain Technology
Blockchain is no longer just about digital currencies; its applications have expanded to include finance, healthcare, logistics, and gaming, among others.
This rapid adoption is driving an unprecedented demand for Web3 developers to build decentralized applications (dApps) and integrate blockchain solutions across various sectors.
- High Demand and Competitive Compensation
The demand for Web3 talent has outpaced supply, making it one of the most lucrative fields in tech. Web3 developers often earn significantly more than traditional developers due to their specialized skills.
Many roles offer remote and flexible working arrangements, enabling global opportunities.
- Opportunities for Innovation
Web3 is still in its infancy, making it a playground for innovators. From creating decentralized finance systems to building virtual economies in the metaverse, developers have the chance to work on groundbreaking projects that redefine industries.
Key Skills for a Successful Web3 Career
To excel as a Web3 developer, mastering certain skills is essential:
- Programming Knowledge: Proficiency in languages like Solidity, Rust, or Go, commonly used in smart contract and blockchain development.
- Blockchain Fundamentals: A deep understanding of how decentralized networks function and their architecture.
- Smart Contracts: The ability to design and implement self-executing contracts.
- Cryptography: Knowledge of encryption techniques to ensure security in applications.
Soft skills such as adaptability and problem-solving are equally important, given the fast-paced nature of the industry.
Benefits of Pursuing a Web3 Career
A career in Web3 comes with a range of unique advantages:
- Global Reach: The decentralized nature of Web3 opens doors to international opportunities without geographical limitations.
- Future-Ready Skills: Web3 expertise is increasingly sought after, offering a secure and sustainable career path.
- Collaborative Ecosystem: Unlike traditional tech environments, Web3 thrives on open collaboration and community-driven development.
- Freedom to Innovate: Developers have the flexibility to experiment and contribute to transformative projects.
Steps to Start Your Web3 Journey
Breaking into a Web3 career may seem challenging, but with a focused approach, it’s entirely achievable. Here’s how to get started:
Understand the Basics
- Learn the core concepts of blockchain technology, decentralized systems, and smart contracts.
- Explore educational resources, tutorials, and online communities for foundational knowledge.
Develop Technical Skills
- Master programming languages and frameworks commonly used in blockchain development.
- Familiarize yourself with Web3-specific tools and libraries to streamline your workflow.
Build Projects
- Start small by creating basic decentralized applications or experimenting with smart contracts.
- Showcase your work in a portfolio to demonstrate your capabilities for a potential employer.
Engage with the Community
- Join forums, developer meetups, and hackathons to network with others in the field.
- Stay updated on industry trends by following Web3-focused discussions and publications.
Continue Learning
- The Web3 space is constantly evolving, so staying up-to-date with advancements is crucial.
- Seek out certifications or courses to deepen your expertise and credibility.
Challenges and Future Outlook
While the opportunities in Web3 are immense, they come with challenges. The fast-evolving technology requires developers to continually upskill. Additionally, the regulatory landscape for blockchain and decentralized systems is still developing, which may introduce uncertainties. A Web3 career offers more than just a job—it provides a chance to shape the next wave of technological innovation. As industries embrace decentralization, the demand for Web3 developers will only grow. Whether you’re a seasoned tech professional or someone looking to enter the field, now is the perfect time to explore this exciting career path. By stepping into the world of Web3, you’re not just advancing your skills—you’re becoming part of a movement that’s redefining how we connect, transact, and collaborate online. The future of technology is here, and it’s decentralized. Will you be part of it?
Technology
Interswitch Advocates AI Adoption for Workforce Evolution

By Modupe Gbadeyanka
The Group Chief Human Resources Officer of Interswitch, Mr Franklin Ali, has called for the adoption of Artificial Intelligence (AI) to make work easier by boosting operational efficiency and driving economic growth.
Mr Ali, at the 2025 InnovateAI Conference Lagos held at the Landmark Centre, Lagos, submitted that, “The AI economy is a gateway to the knowledge economy, and it is imperative that we embrace this shift.”
“While AI adoption in leading economies like America and China remains below 50 per cent, these nations are at the forefront of AI advancements.
“To compete globally, Nigeria must prioritise reskilling and upskilling its workforce, fostering a mindset shift, and equipping professionals with core and enabling skills such as data literacy, JavaScript, and other technical competencies,” he further stated during a panel session titled AI and The Future of Work in Nigeria.
The Human Resources expert while emphasising the importance of targeted learning and problem-solving at the event themed Scaling AI Adoption in Nigeria: Catalysing Cross-Sectoral Innovation and Fostering Inclusive Growth, informed the participants that, “AI is not just a buzzword; it is a tool for solving real-world problems.”
“For instance, traffic congestion in Lagos is a challenge that can be addressed through AI-driven solutions.
“However, adept use of AI technology requires a deep understanding of core tech skills in areas like natural language processing, robotics, and machine learning.
“We must learn AI not for the sake of it but to solve specific problems that impact our society and economy,” he noted.
This year’s conference had Interswitch Group as a Platinum Sponsor for the second consecutive year, reinforcing its commitment to advancing AI-driven innovation across Africa.
By collaborating with key stakeholders and fostering industry-wide conversations, Interswitch aims to drive AI-powered innovation that will propel Nigeria’s digital economy forward.
As a pioneer in Africa’s fintech space, Interswitch remains dedicated to championing initiatives that harness technology’s transformative potential to unlock new opportunities, stimulate economic growth, and elevate user experiences.
Technology
YP4T Tasks Nigeria to Explore Opportunities in Digital Economy

By Aduragbemi Omiyale
The Nigerian government has been charged to quickly tap into the opportunities in the digital economy to help achieve the $1 trillion economy target of the administration of President Bola Tinubu.
This call was made by the Young Professionals for Tinubu (YP4T), which expressed delight over the willingness of the federal government to embrace artificial intelligence (AI).
The group warned that Nigeria must sustain these efforts to fully unlock the potential of AI-driven growth.
With a youth population expected to exceed 100 million by 2050, ensuring that young professionals have the skills, tools, and infrastructure to build AI-powered solutions is key to job creation and economic stability.
“As a network of young professionals actively engaged in shaping Nigeria’s future, we see these investments as fundamental to building a globally competitive workforce.
“This is not just about innovation; this is about securing economic opportunities for millions of young Nigerians. AI and digital transformation must be central to Nigeria’s long-term growth strategy, and every young Nigerian should be paying attention to these opportunities,” the Director of YP4T for West/South South, Mr Victor Benjamin, Stated.
“AI is no longer a theoretical concept—it is a defining force in global economies, and Nigeria is now actively securing its place in that future.
“For years, young Nigerians have sought opportunities in technology and digital innovation. What we are seeing now is a deliberate effort by the administration to turn that aspiration into reality through strategic policies, funding, and industry collaboration.
“This is a critical time for Nigerian professionals and businesses to position themselves in the AI-driven economy,” he added.
It has been projected that AI could add about $15 billion to the GDP of Nigeria if well-harnessed by the government through policies.
Recall that last week, Mr Tinubu held high-level discussions with the chief executive of Google, Mr Sundar Pichai, in France.
Talks also centred on the federal government 3 Million Technical Talent (3MTT) initiative, which has already begun producing a pipeline of AI-trained professionals, while the National AI Strategy Framework has laid the groundwork for AI integration across finance, agriculture, healthcare, and education.
Technology
Best Practices for Keeping Your CMS Updated and Secure
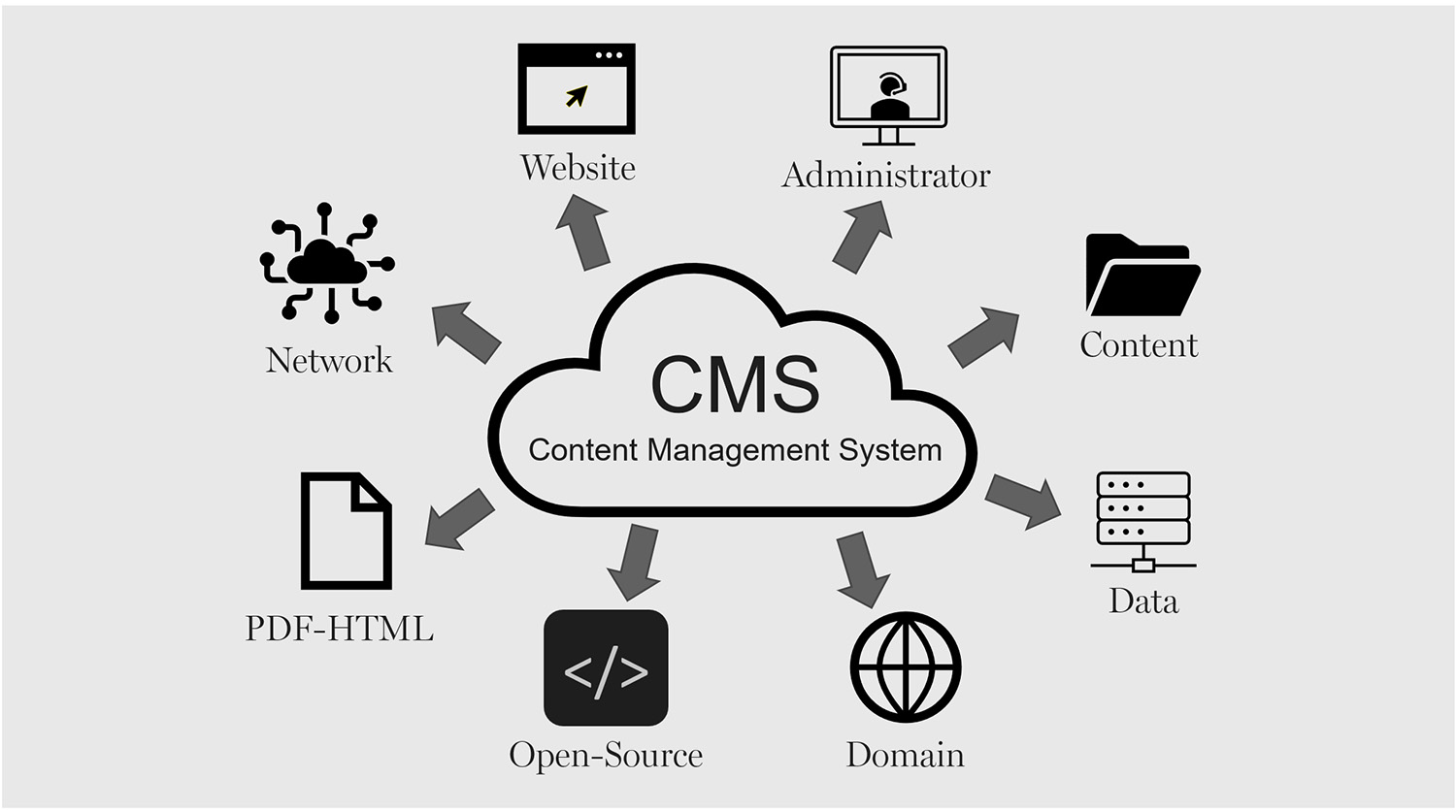
A Content Management System (CMS) drives many websites as it offers the best creation, maintenance, and deployment of digital content for an expanding enterprise. However, CMS can be an issue if not regularly updated or if security patches are bypassed. When hackers realize a CMS version is vulnerable, they attempt to breach it, gaining entry into a system to steal information or shut down a website.
A secure and reliable headless CMS requires constant updating, specific log-in and access, and continuous monitoring. Thus, a business that requires a secure CMS will ensure that client information is kept private, the experience is overall more seamless, and compliance is easier. This article outlines all the necessary updates and security patches to keep a secure and reliable CMS.
Regularly Updating CMS Core, Plugins, and Themes
One of the quickest ways to eliminate security vulnerabilities is by keeping the headless CMS core software and plugins/themes up to date. Developers are always updating for security vulnerabilities, enhancements of functionality, and added features. Failing to keep current opens a portal of exploitation for sites that developers have already fixed, making these sites low-hanging fruit for hackers. For example, if a retail business has a WordPress CMS for its website, and the WordPress CMS is outdated, it opens the site to being hacked.
There are WordPress fail issues that have not yet been addressed, which give hackers the chance to enter the system and add in malware. If a site has a lot of pending updates, many security vulnerabilities can be prevented. By checking often or setting up automatic updates, any business will have the most secure system possible. In addition, plugins or themes that are no longer supported by developers are ones to avoid as well. An unsupported plugin—with or without updates is a vulnerability, and it should be changed for something that gets consistent updates.
Strengthening Authentication and Access Control
A headless CMS such as the one that Storyblok provides usually has multiple users with different access levels. From administrators and editors to simple content creators, everyone can be a guest on the CMS. However, without access controls, a standard user can be granted administrative privileges either accidentally or on purpose and delete information or leave the CMS open for attack or intentional editing. Access control authorization relies on authentication. The ultimate protection for a CMS is multi-factor authentication. Multi-factor authentication reduces the likelihood of an account being compromised because it requires another form of validation aside from a username and password.
These can include one-time passwords or biometric fingerprints. Furthermore, implement super admin access to only what is necessary. If many team members need access to a project, role-based access (RBAC) gives everyone access only to what their job requires. The fewer the super admin accounts, the fewer the chances of insider threats and accidental security misconfiguration. Furthermore, the company should have password policies in place to require complicated passwords capitalization, numbers, special characters and employees should be educated on changing their passwords regularly. The chances of credential compromise are minimized with password managers.
Using Secure Hosting and Encrypted Connections
A headless CMS is only as good as its hosting. Should a company choose a reliable hosting service that includes security (firewalls, DDoS protection, malware scanning along with proper backup solutions), the company can maintain a secure level from the very beginning. On the other hand, unreliable hosts are vulnerable and subject to server-level attacks, which leave a site vulnerable to hacks and shutdowns. Another major component of security is a Secure Socket Layer (SSL) certificate, which protects all information sent from users to the site from prying third-party eyes.
With SSL encryption, this allows a company to avoid handing over to hackers any passwords, compromised personal information, or credit card numbers during those vulnerable transactions. Companies that deal with sensitive customer information needing additional security may opt for a managed hosting service with built-in, automated security management. Managed hosting services are more likely to secure vulnerabilities, watch for nefarious activity, and perform security hardening so these companies don’t have to delegate duty.
Conducting Regular Security Audits and Vulnerability Assessments
Regular security audits and vulnerability scans uncover vulnerabilities in a headless CMS before a hacker gets the chance to exploit them. Security audits ensure correct user permissions, potential database corruption, and server configurations so that no unintended levels of access exist. For example, a content-managed eCommerce site should assess how often rogue administrators can access the CMS via security audits to avoid malicious penetration that could lead to poor choices. Thus, a content-managed eCommerce site wants to ensure that accidental charge transactions do not happen on the checkout function, so a vulnerability scan is regularly required.
Security plugins within the headless CMS and external vulnerability scanning websites provide assessments of malware injections, brute force login attempts, and unnecessary file permissions. Furthermore, simply keeping an eye on the CMS logs to check for oddities, surprising login attempts, changes in core files, individuals visiting the admin panel when they should not be granted visibility would keep a company apprised of its security. An apprised awareness of security would avoid a lot of exploits from escalating into a massive cybersecurity event.
Implementing a Reliable Backup Strategy
Fail-safe backup solution. Even with the most secure CMS, there’s always a chance that a hack or malfunctioning headless CMS occurs or even a wipe happens accidentally. A backup solution that is fail-safe ensures that no matter what type of catastrophic security issue occurs on the site, it can be restored with ease and no major downtime. Backup should be automatic and regular, off-site or an encrypted cloud solution. This ensures that even if the primary server is hacked, nothing is lost. A backup solution should encompass full database, full file, and full configuration backups for the CMS to guarantee that everything is restorable when needed.
For example, a headless CMS-centric, news-driven site and a digital asset manager are hacked and all posts are erased. They’ll be restored in a flash unless the backup from last night is still there. These types of restorations need to be regularly tested to confirm they are there and up to date.
Securing API Integrations and Third-Party Extensions
Many CMS have third-party applications, payment processors, and other services via API integrations for extended functionality. However, these integrations are potential weaknesses that hackers can infiltrate without proper security protocols. All API integrations should require secure authentication encrypted API keys and OAuth tokens and unauthenticated services should never have unrestricted access to sensitive data. Furthermore, only externally developed plug-ins and extensions should be used and those created by trusted developers and extensively vetted; antiquated, unpoliced third-party applications can open disastrous loopholes.
Of course, being a financial center, a headless CMS for investment and sourcing and getting reputable user information should have all third-party APIs and financial integrations assessed for security compliance to prevent data leaks or accidental purchases. By assessing and strengthening these external integrations, companies reduce the risk that additional vulnerabilities will penetrate the CMS ecosystem from the outside.
Monitoring and Responding to Cyber Threats
Yet regardless of how bulletproof a site may be, the ideal method of learning about and addressing cybersecurity weaknesses will always be preemptive and responsive awareness. Thus, companies need to adopt further real-time security monitoring to be notified of nefarious actions, unauthorized logins, and breaches. For example, a retail website’s enterprise content management system should include intrusion detection systems (IDS) and web application firewalls (WAF) to prevent accidental access from those who don’t belong or to prevent interactions with bots.
In addition, a cyber incident response plan ensures that there are trained protocols for rapid response if a breach were to happen. For instance, an incident response plan dictates that one must quarantine affected machines, roll back to backups, notify stakeholders, and determine how to prevent this from happening again. This level of understanding empowers organizations to be ahead of the game and mitigate as much destruction to their content management systems that cyber intrusions would create.
Conclusion
A maintained, safe CMS is not static. There are security updates, there is testing and debugging, and vulnerabilities are always there. Thus, for these enterprises that fail to secure their CMS systems, the chance for attacks is great resulting in breaches and costly downtime, which creates not only chaos in brand identity but in the company’s balance sheet. These measures minimize exposure and build a resilient, secure environment when organizations change default CMS files, update passwords, enhance server security, and engage in security audits.
Secure API integrations, knowledge of cybersecurity developments, and the ability to restore backups reliably, create a CMS more resistant to ever-increasing threats. A secure Content Management System essentially protects vital proprietary and customer data and keeps sites up and running with appropriate user confidence. Firms with a comprehensive Content Management System security strategy render their businesses transferable to the digital arena with more growth potential and less concern for cyber attacks.
-

 Feature/OPED5 years ago
Feature/OPED5 years agoDavos was Different this year
-
Travel/Tourism9 years ago
Lagos Seals Western Lodge Hotel In Ikorodu
-

 Showbiz2 years ago
Showbiz2 years agoEstranged Lover Releases Videos of Empress Njamah Bathing
-

 Banking7 years ago
Banking7 years agoSort Codes of GTBank Branches in Nigeria
-

 Economy2 years ago
Economy2 years agoSubsidy Removal: CNG at N130 Per Litre Cheaper Than Petrol—IPMAN
-

 Banking2 years ago
Banking2 years agoFirst Bank Announces Planned Downtime
-

 Sports2 years ago
Sports2 years agoHighest Paid Nigerian Footballer – How Much Do Nigerian Footballers Earn
-

 Technology4 years ago
Technology4 years agoHow To Link Your MTN, Airtel, Glo, 9mobile Lines to NIN